
Traditional container images inherit a large number of packages from their base distribution. These packages often include utilities, libraries, and system components that are not required by the application but still remain part of the image. While they may not be actively used by the application, they increase the overall attack surface and can introduce additional vulnerabilities.
Minimus images take a different approach by building minimal, distroless runtime images that contain only the packages necessary for the application to run.
To make this difference easy to visualize, Minimus includes a Package Count & Risk Comparison between the Minimus image and the corresponding public image. This comparison highlights how many packages are included in each image and shows how much unnecessary software has been removed.
In many cases, the difference is significant. A typical public image may contain hundreds of packages inherited from the base operating system, while the Minimus image contains only the minimal set required at runtime.

For example, the public node image contains over 500 packages, while the Minimus node image includes only a few dozen packages. These remaining packages consist of essential runtime components such as core libraries, certificate bundles, and minimal system utilities required by the application.
The Minimus package count view can be found inside the “Risk Reduction” tab for each Minimus image. Each square represents a single package included in the image. This makes it easy to immediately see the scale of the difference between the Minimus and public images.
In the public image section, packages are also separated between the base layer and additional layers. The base layer represents the operating system packages included in the image, such as system libraries and core utilities. Additional layers represent packages introduced when the image is built or extended for a specific application. This view helps illustrate how container images accumulate software components and where most of the packages in the image originate.
Each package in the comparison is also color-coded according to the highest severity level of the vulnerabilities associated with that package, making it easy to identify which components introduce higher security risks.
The Minimus package Visualization allows users to quickly see not only how many packages exist in the image, but also how security risk is distributed across those components.
In addition to the package visualization, Minimus also provides a detailed package comparison for each image. This view shows every package included in the Minimus image and the corresponding public image, along with the number of vulnerabilities affecting each package.
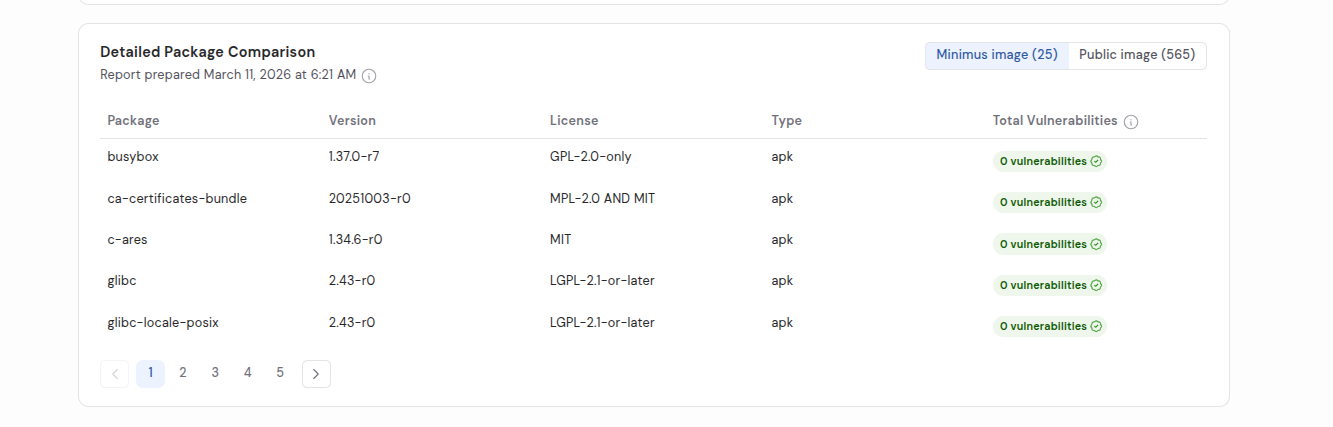
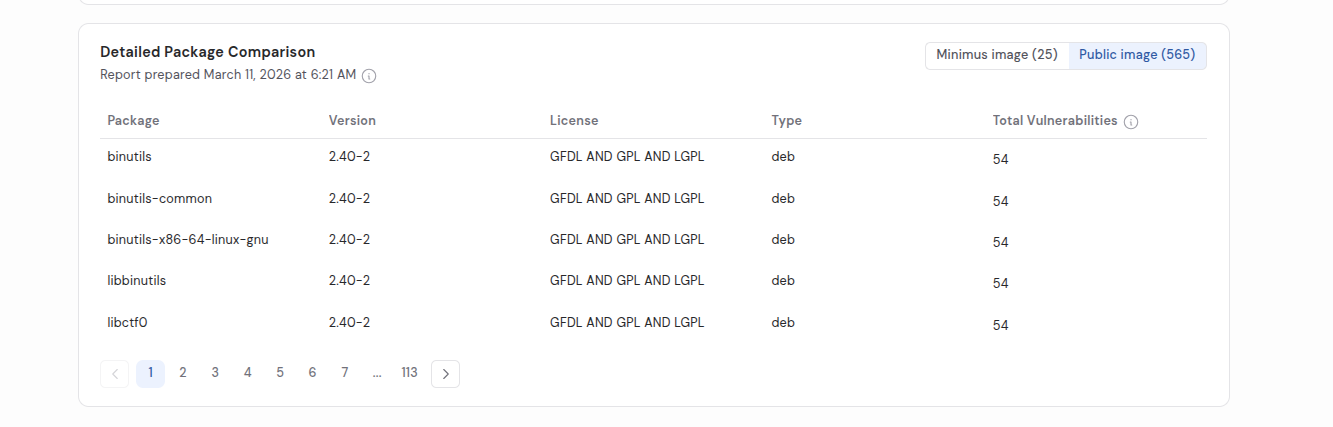
This makes it possible to examine not only the total number of vulnerabilities in an image, but also which packages introduce them.
To illustrate this difference, the table below compares several images and highlights the differences in package count and current vulnerability exposure between Minimus images and the corresponding public images.
By reducing the number of packages included in the runtime environment, Minimus images remove large portions of unnecessary dependencies and components that could introduce vulnerabilities. Request a demo to explore how these container runtime differences apply to your own workloads.