NIST SP 800-190 RECOMMENDATION
HOW MINIMUS IMAGES SUPPORT IT
IMAGE PROVENANCE VERIFICATION (5.1.2)
Minimus implements SLSA L3 compliance, providing signed, non-repudiable attestations to verify the image origin, build process, and source integrity.
USE MINIMAL BASE IMAGES (5.1.4)
Utilizes a distroless-like base, eliminating the shell and package management layer. This removes unnecessary packages and binaries, fulfilling the principle of least privilege in the image itself.
SCAN IMAGES FOR KNOWN VULNERABILITIES (5.1.6
Automated tooling continuously scans images for new CVEs and triggers automated rebuilds and patch delivery, ensuring continuous vulnerability management and system patching.
LIMIT CONTAINER PRIVILEGES (5.3.1)
Images are configured to run as a non-root user by default, lacking shell access (/bin/sh or similar). This configuration enforces a least-privilege security posture at runtime.
PROTECT SECRETS AND SENSITIVE DATA (5.4.1)
The immutable and minimal nature of the images prevents secrets sprawl and ensures that secrets or credentials are never inadvertently baked into the image layer itself.
USE TRUSTED REGISTRIES (5.2.1)
Images are delivered via a private, secure registry that supports traceable updates and verifiable provenance data for integrity checking prior to deployment.
LIFECYCLE MANAGEMENT OF CONTAINERS (5.5.2)
Minimus enforces a strict rebuild and patch delivery cadence to ensure ongoing compliance with lifecycle security requirements, minimizing the window of exposure.
ENFORCE RUNTIME SECURITY CONTROLS (5.3.2)
Images leverage pre-hardened kernel configurations and security profiles, which significantly minimizes the need for complex, post-deployment security tooling.
AUDIT CONTAINER EVENTS (5.6.1)
Complete Software Bills of Materials (SBOMs) and rich metadata are generated for every build, providing full traceability and compliance-friendly audit trails for deployed containers.
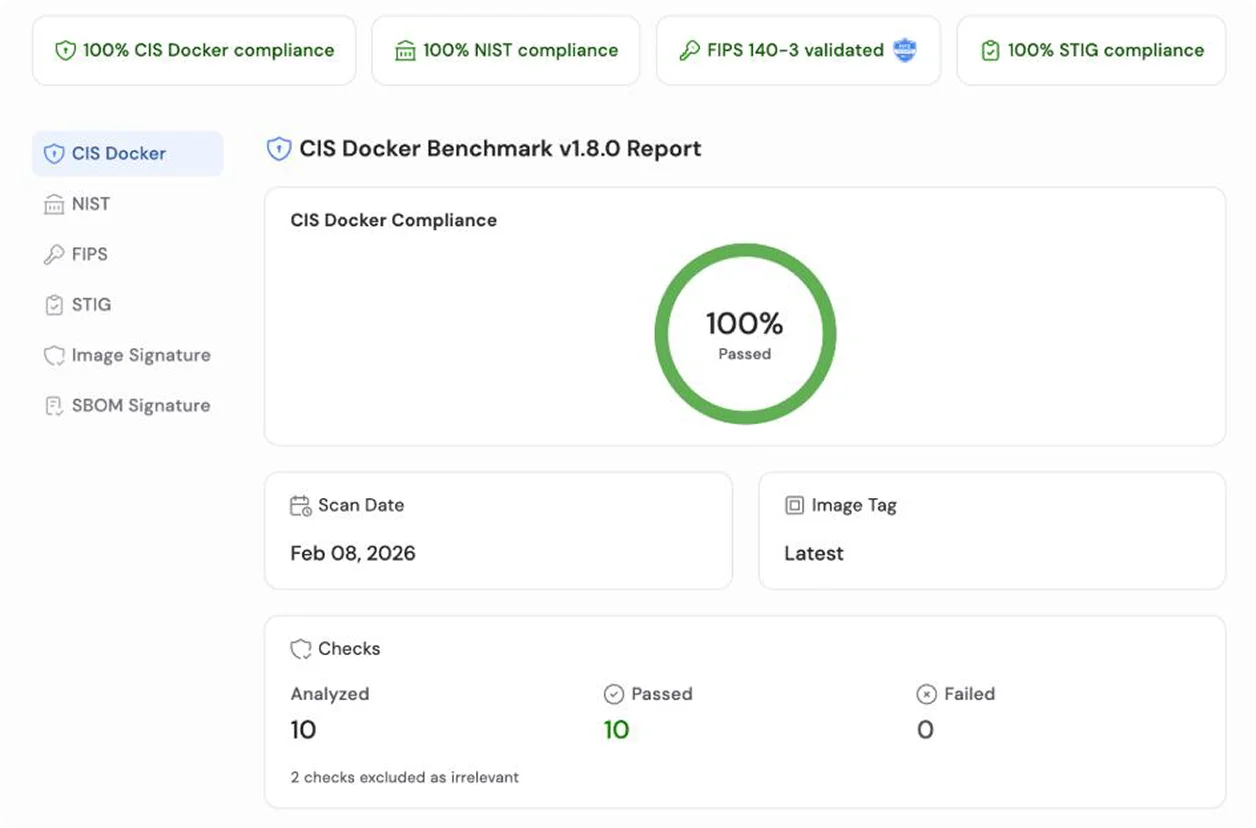
COMPLIANCE DOCUMENTATION (3.1)
The Minimus NIST Report provides provable, per-build compliance documentation against Section 3.1, giving auditable evidence for relevant NIST IDs