Minimalist Image Architecture Reduces CVEs by 97%+
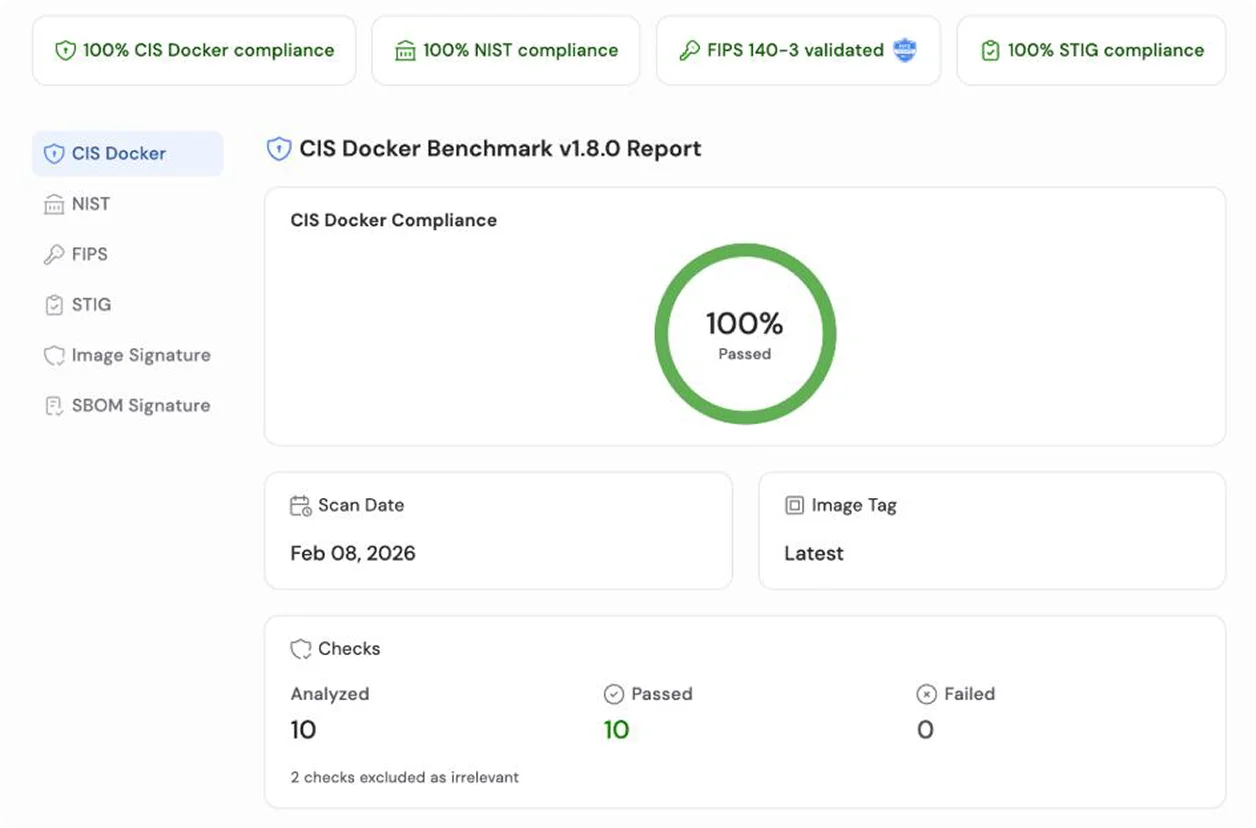
Minimus images employ a distroless model, incorporating only the essential runtime dependencies of a specific application. By systematically eliminating non-essential components such as package managers, shells, and compilers, Minimus drastically reduces the attack surface and simplifies the process of achieving image-level compliance with FedRAMP, CIS benchmarks, and NIST SP 800–190.