
All applications have historically come with their own costs to build, test, and operate; and applications built based on container images are no different. While the main benefit of distroless minimal images is that they reduce the vulnerability and attack surface footprint for applications running in containers, a common side benefit is a reduction of the image size.
In this blog, we’ll focus on the material and scale benefits of adopting minimal distroless container images outside of security advantages.
There are many infrastructure costs that need to be considered throughout the software development lifecycle for applications running in containers.
Direct correlations between smaller image size and reduced infrastructure costs include:
Even small reductions in image size can compound significantly across hundreds or thousands of builds, pulls, and deployments per day. With minimal image providers like Minimus, where images are often dramatically smaller than public equivalents, this compounding effect is amplified, multiplying savings across storage, transfer, compute, and pipeline execution at scale.
Container images are routinely pulled across developer laptops, CI runners, staging, and production clusters, often dozens or hundreds of times per day for troubleshooting, application sharing, and other day-to-day operational uses.
Smaller images pull and load faster, because less data moves across the network and is written to disk. In CI environments that start from clean runners, this is measurable in seconds per build. Across parallel pipelines and repeated executions, those seconds translate into shorter pipeline durations and lower infrastructure utilization.
For example, a 300MB reduction pulled 100 times per day equals 30GB less data transferred daily, or 900GB per month for a single image. If five services each experience the same 900GB monthly reduction, that equates to 4.5TB less data transferred per month. At typical cloud egress rates (e.g., $0.09 per GB), that alone could represent roughly $400 in monthly bandwidth savings, excluding additional compute and time efficiencies.
These savings also translate directly into improved engineering productivity and capacity. Faster pulls and shorter pipelines reduce engineer wait time and deployment friction, converting seconds saved per build into reclaimed engineering hours each week across multiple teams.
As container images are built and shipped, images are also generally subject to constant load through automation. This includes:
Base images are often reused as the foundation for many other images, increasing the impact of the above at an exponential level. In practical terms, this means image size affects::
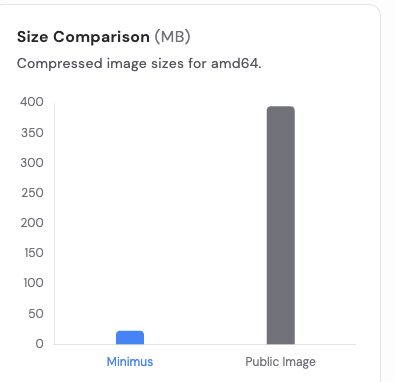
Below is a size comparison of Minimus images versus their public equivalents:
Across the ten images shown, the median reduction is approximately 141%, with an average reduction of 371% (skewed higher by extreme reductions such as Python). While not every image is drastically smaller, the majority demonstrate substantial size reduction that directly impacts storage, transfer, and pull performance at scale.
In many cases, the size difference is not incremental, it is exponential. Images such as Python, Node, and nginx show multi-hundred percent reductions in size:
nginx:

python:
Moving to distroless minimal images is not just about security. It is about operational leverage. By reducing image size, organizations decrease infrastructure consumption, accelerate CI/CD workflows, improve deployment speed, and compound efficiency gains across environments.
Minimus images extend the value beyond size alone. Additional benefits over many public variants include:
If you’d like to see how these efficiencies translate within your own environment, request a demo to explore Minimus in action.