FedRAMP Security Standards
The Federal Risk and Authorization Management Program (FedRAMP) establishes stringent requirements for cloud service providers and contractors supporting U.S. federal agencies, particularly around system integrity, vulnerability management, configuration baselines, and secure DevOps.
Minimized Attack Surface
Minimus container images are designed to align directly with these objectives. Built from scratch with only essential components, Minimus images reduce vulnerability exposure by 97% or more compared to common base images.
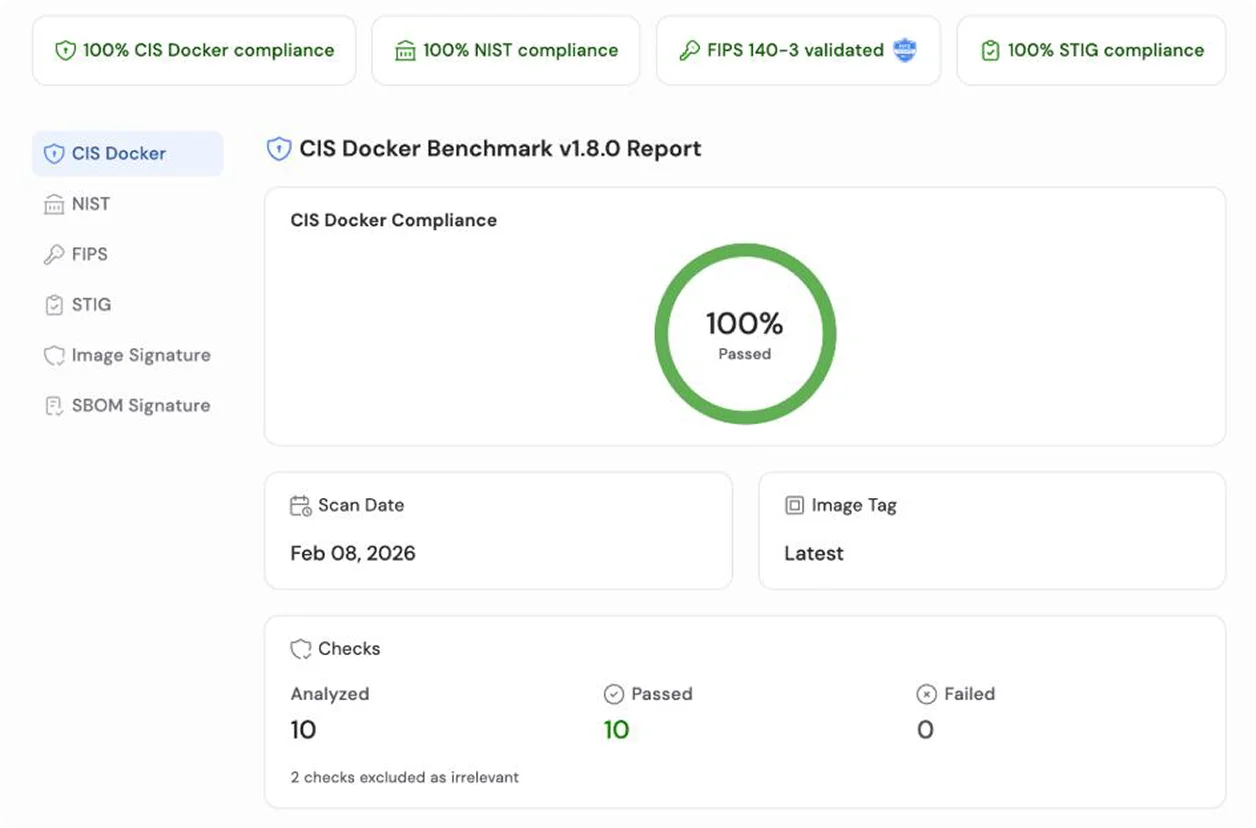
Built for Compliance
This hardened baseline, combined with integrated threat intelligence for CVE prioritization, support for automated remediation via action providers (e.g., Slack, GitHub Actions, and webhooks), native scanner support (e.g., AWS Inspector, Snyk, Trivy, Grype), and full compatibility with self-hosted and air-gapped environments, makes Minimus a powerful enabler for FedRAMP-compliant containerized workloads.