
Observability is a key tenant of security, and security teams want eyes everywhere. While Minimus doesn’t process or store our customers’ data in our platform, it doesn’t mean there’s nothing critical happening. Security organizations can use Minimus’s Activity Log to monitor platform access and configuration changes that affect their security posture.
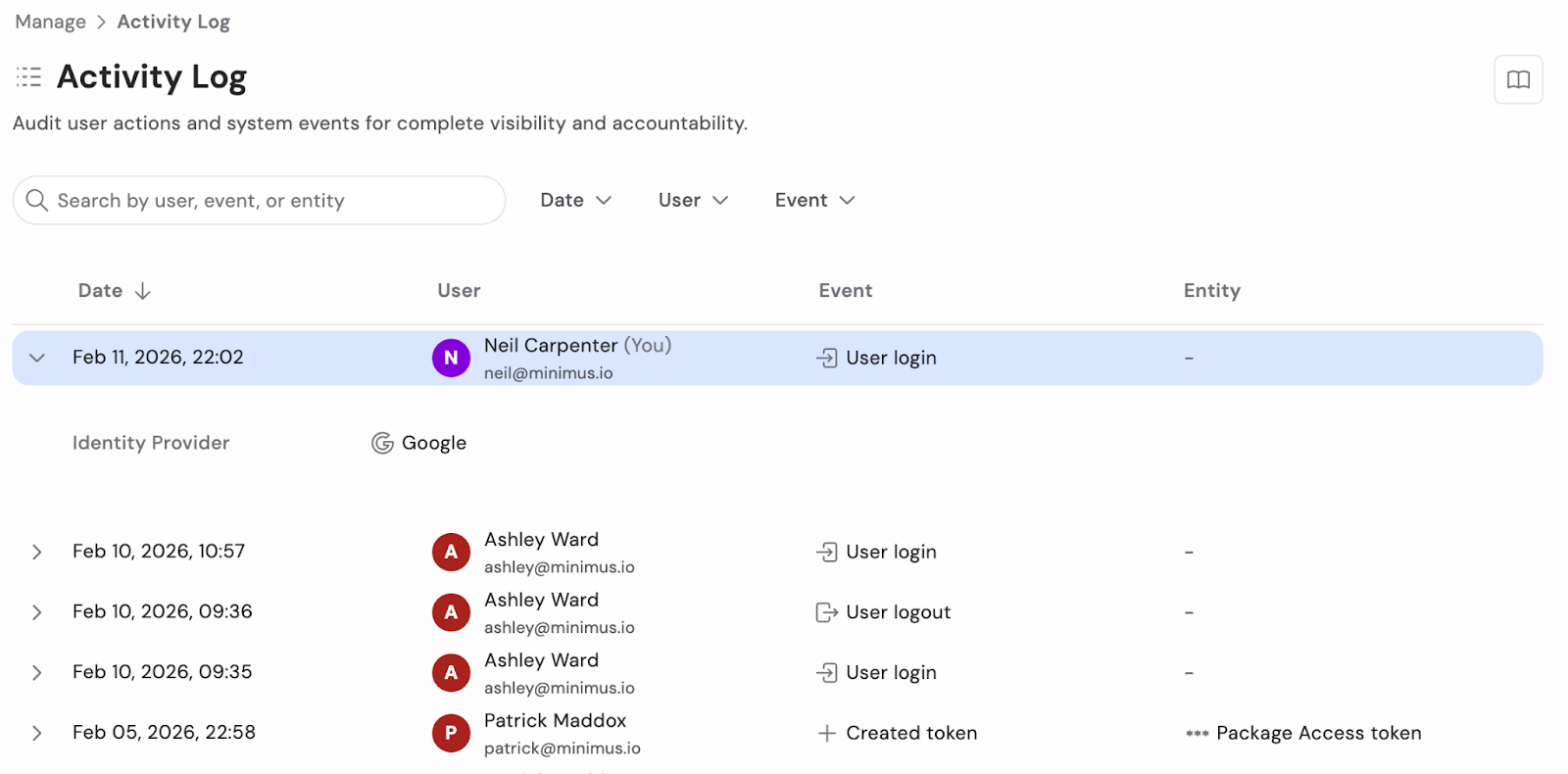
First, the Activity Log allows administrators to monitor logins to the platform, enabling them to see who is using the Minimus console. While most users may consume Minimus images in pipelines and deployments without ever needing the console, it remains an important tool for developers and other engineers to research available container images, Helm charts, and other collateral. Having login data readily available ensures that administrators know who is accessing the console.
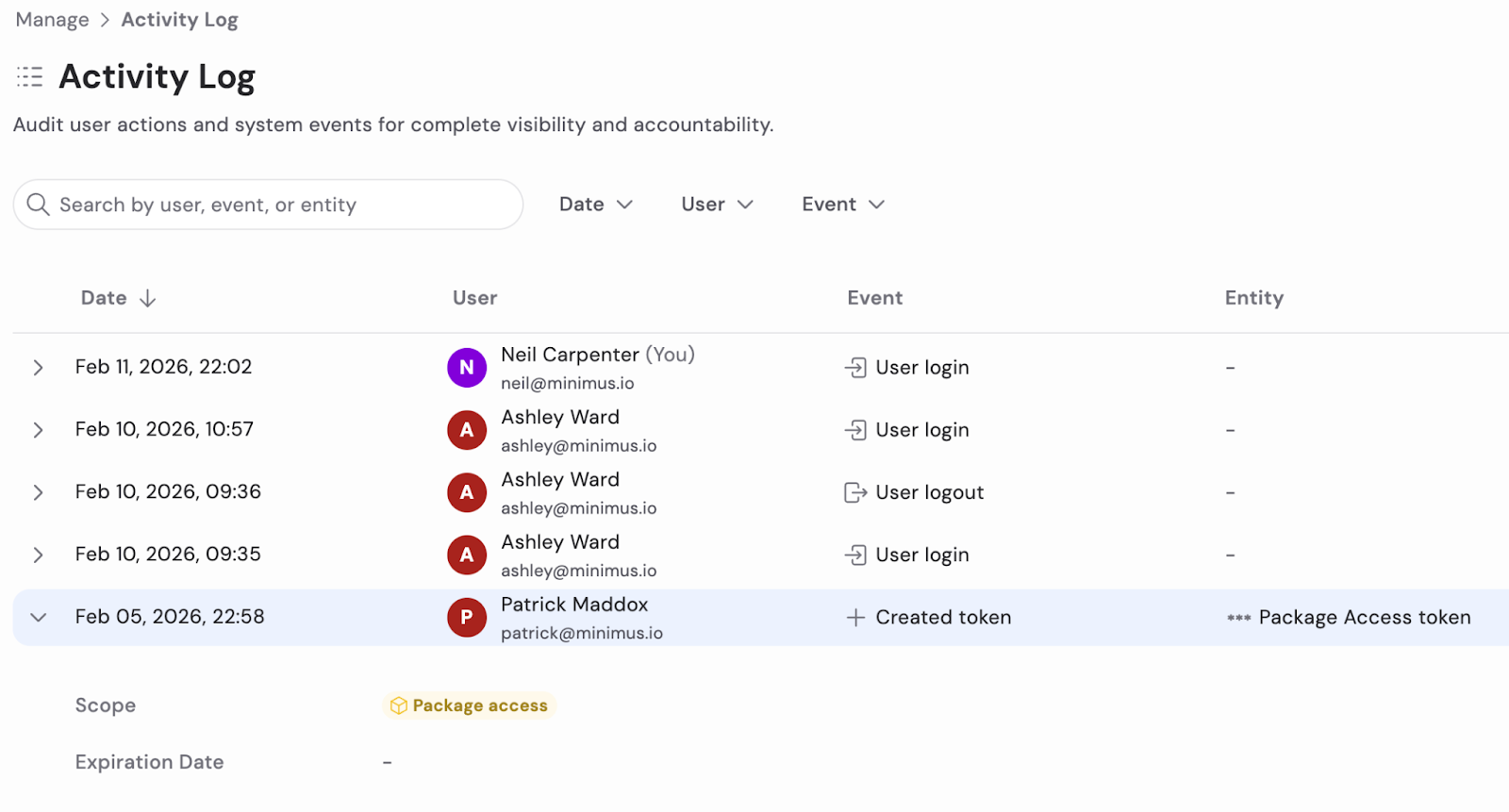
Access is not the only thing that may be of interest. Token management can be tracked and audited in the Activity Log, ensuring that administrators know who created and deleted tokens. (Of course, only users with the Operator role or better can create and delete tokens to begin with.)
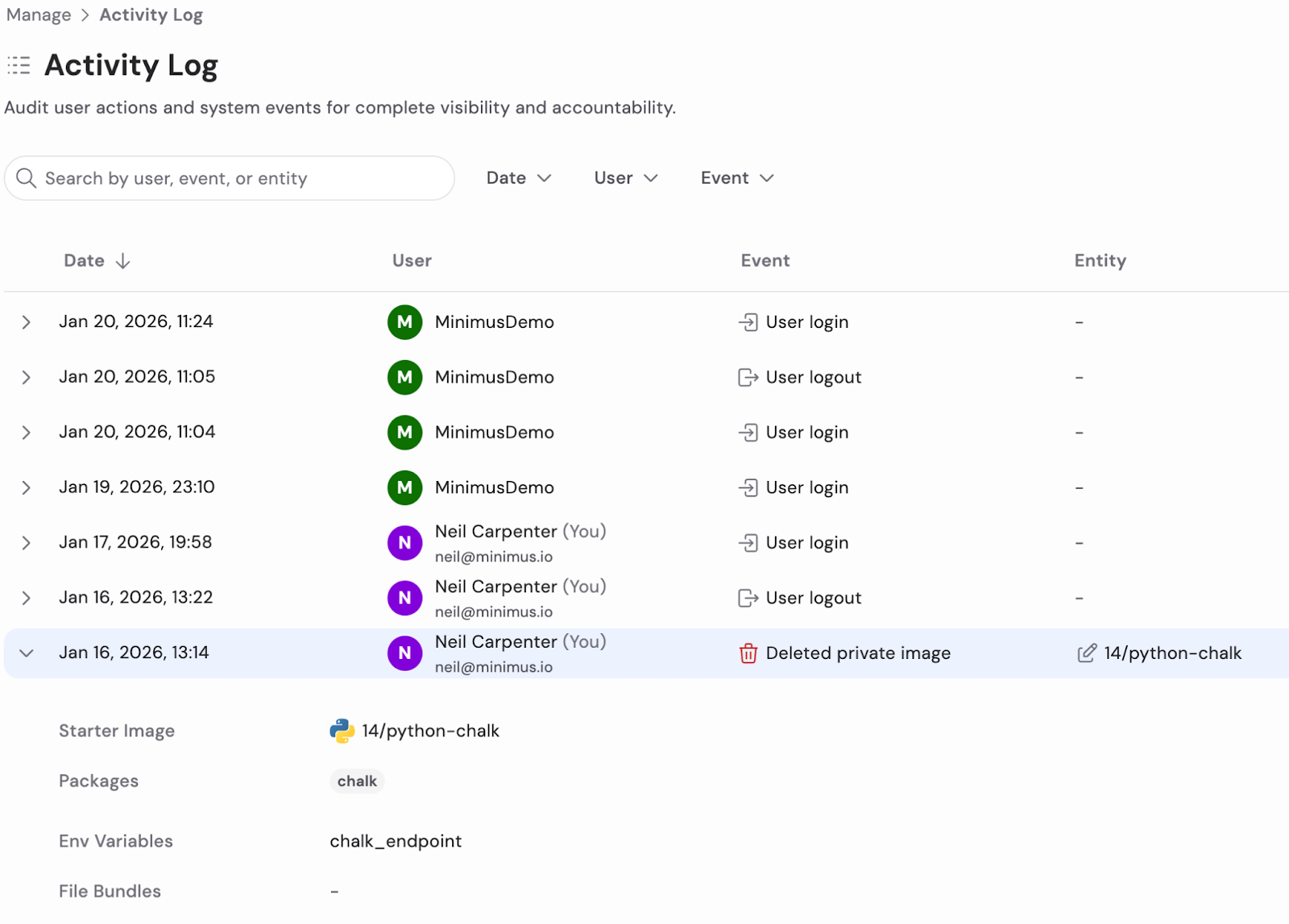
Another example of when administrators might want to consult the Activity Log is the creation and deletion of custom images in Image Creator. This functionality allows organizations to build bespoke base images tailored to their requirements and environments.
Creating custom images requires, once again, at least the Operator role. If a custom image is inadvertently removed, it could result in pipeline failures or deployment issues. The Activity Log allows an administrator to determine who performed the action, what changed, and when it occurred, making it easier to troubleshoot and remediate.
In summary, the Activity Log gives Minimus administrators peace of mind in being able to audit and track both access to the Minimus console and impactful configuration changes. The centralized audit trail for logins, token activity, and image management makes reviews, change tracking, and operational accountability easy.