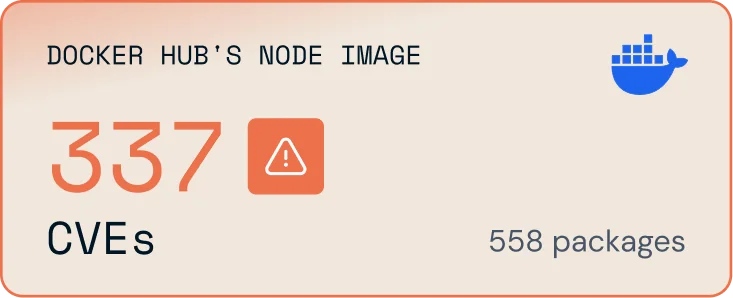
Reverse engineering a CVE used to take skill, time, expertise. Now? It takes a prompt.
Attackers are moving faster than the open source supply chain can keep up
Traditional prioritization and patching strategies no longer scale
Zero CVE is becoming the baseline, and Minimus enables it
Minimus images are hardened. Even if an AI agent breaches your perimeter, it's trapped. No shells. No network utilities. No tools. Nothing to work with. Simple, minimal, secure by building from the ground up.
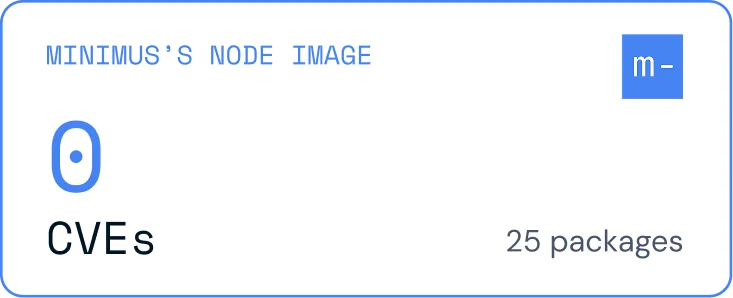
All upstream fixes applied at build time. Zero known CVEs at delivery, contractually guaranteed, with a 48-hour remediation SLA for newly disclosed vulnerabilities. Nothing left to chain together.
Only the runtime dependencies your application needs. Shells, package managers, and network utilities stripped entirely. Built from source continuously. OCI-compliant, with FIPS 140-3 modules available.
Provable compliance with CIS, NIST, and STIG benchmarks for every image. Automated testing and documented results per build. Supports FedRAMP, DORA, and NIS2 posture requirements.
Real-time threat intelligence from EPSS, CISA-KEV, and Minimus Labs. Prioritize upstream vulnerabilities by actual likelihood of exploit, not just CVSS score.
Automatically trigger events in Slack, Jira, GitHub, and more. Built in enterprise-grade integrations and alerting. Designed for SecOps workflows at scale.
Pull from the registry of your choice. Fully air-gapped support available. Hardened Helm Charts, native and versioned by Minimus. Works where your stack lives.

Detection tools find vulnerabilities but leave remediation to your team. When an AI exploits any known CVE instantly, alerts are too slow to matter.

Detection tools find vulnerabilities but leave remediation to your team. When an AI exploits any known CVE instantly, alerts are too slow to matter.

Detection tools find vulnerabilities but leave remediation to your team. When an AI exploits any known CVE instantly, alerts are too slow to matter.

Contractual guarantee that images arrive with all upstream fixes applied, plus a 48-hour SLA when new vulnerabilities are disclosed. Nothing to chain together.

Distroless images contain only what your app needs. Even if an agent gets in, there are no shells or utilities to execute a 32-step network takeover.

Trusted by global financial institutions and startups alike. Backed by SOC 2 Type II and ISO/IEC 27001 certifications.















