One of the most important aspects of proactive security is staying compliant. The problem today is that most teams build using bloated public images that are not compliant by default. They then have to strip out unnecessary packages, configure images to meet standards, maintain that posture over time, and provide evidence for auditors. This process is time-consuming, difficult to scale, and often leaves gaps in visibility.
Knowing that the foundations of your container infrastructure are configured and compliant by default makes compliance much easier. Minimus provides hardened, compliant images, keeps them continuously maintained, and gives you everything you need to demonstrate compliance across development and audit workflows.
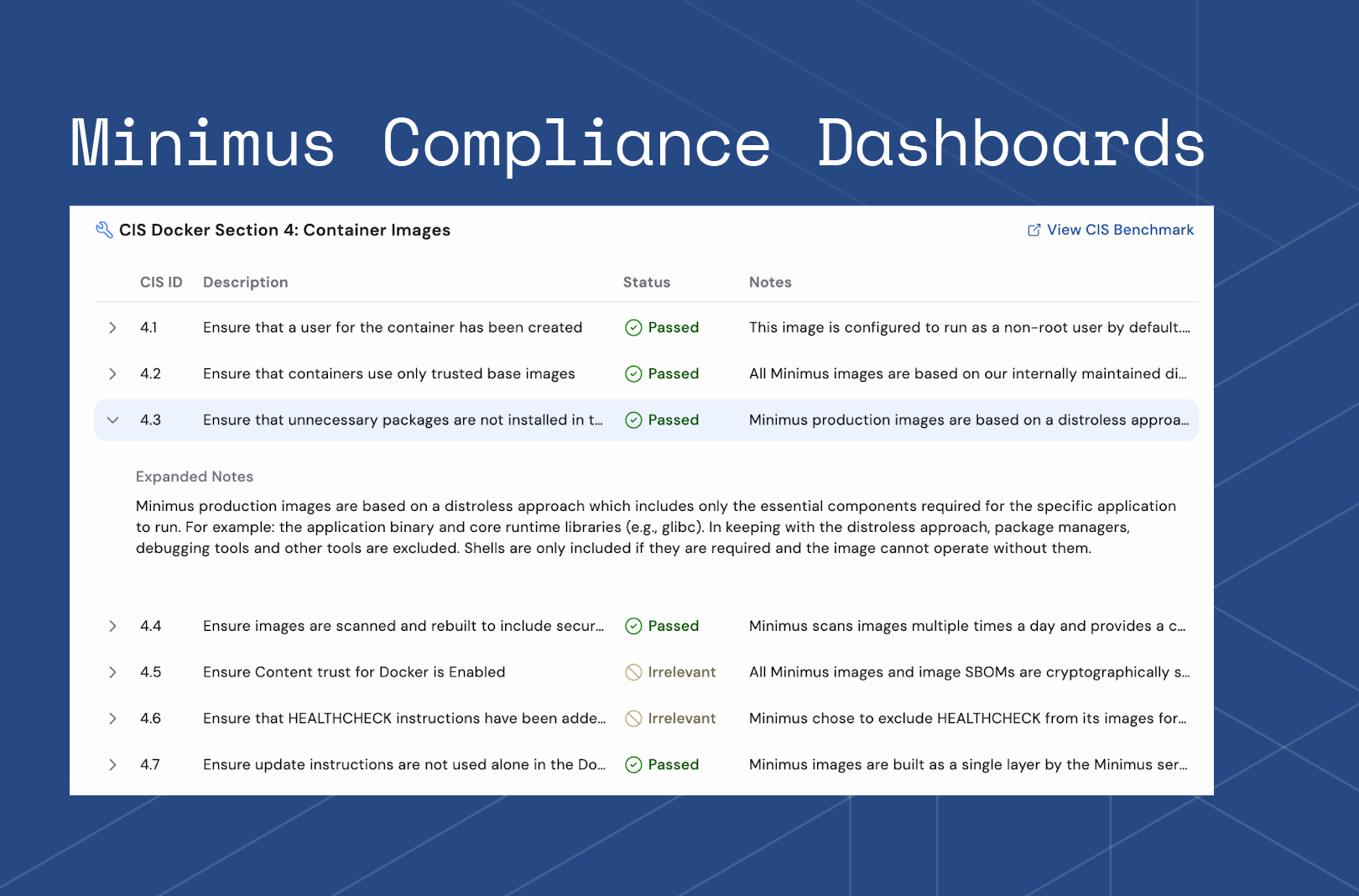
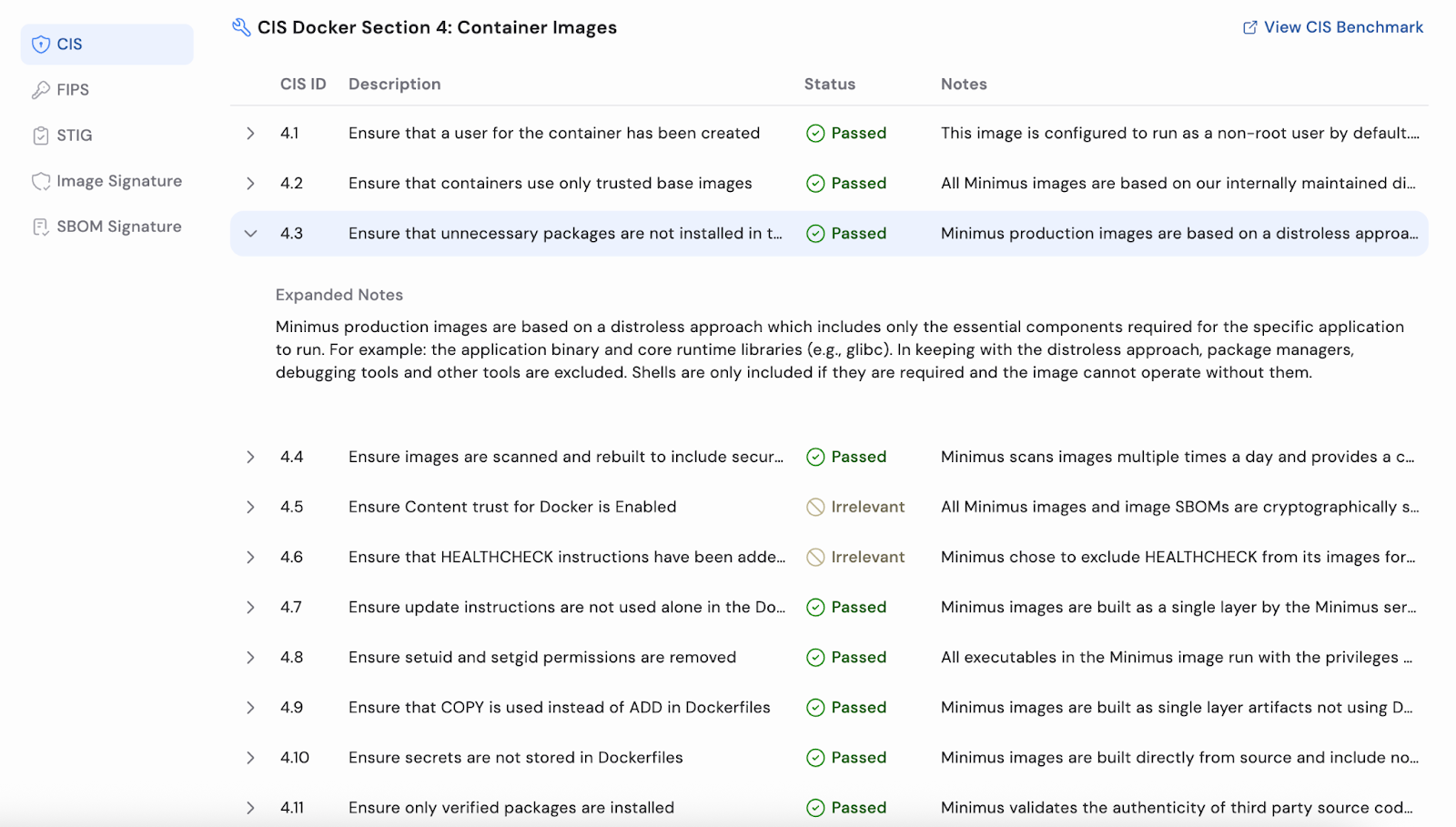
Minimus’ compliance dashboards give you clear visibility and detailed insight into how our images measure against CIS, FIPS, and STIG standards, all directly in the Minimus UI.
Combined with our built-in vulnerability reduction, this enables customers to deploy more durable infrastructure that stays resilient over time, with compliant images that are continuously maintained and ready for both development and audit workflows.
Minimus customers can now view at an image level, or across their environment, the specific compliance regimes and controls image configurations are mapped to.
These views make it easy to:
Compliance details are available for every single image Minimus produces, including private images.
To access the compliance details for an image, you can navigate to the specific image and select the Compliance tab. Reports are available for the CIS benchmarks, FIPS, and STIG, as well as instructions on how to verify and validate the configurations.
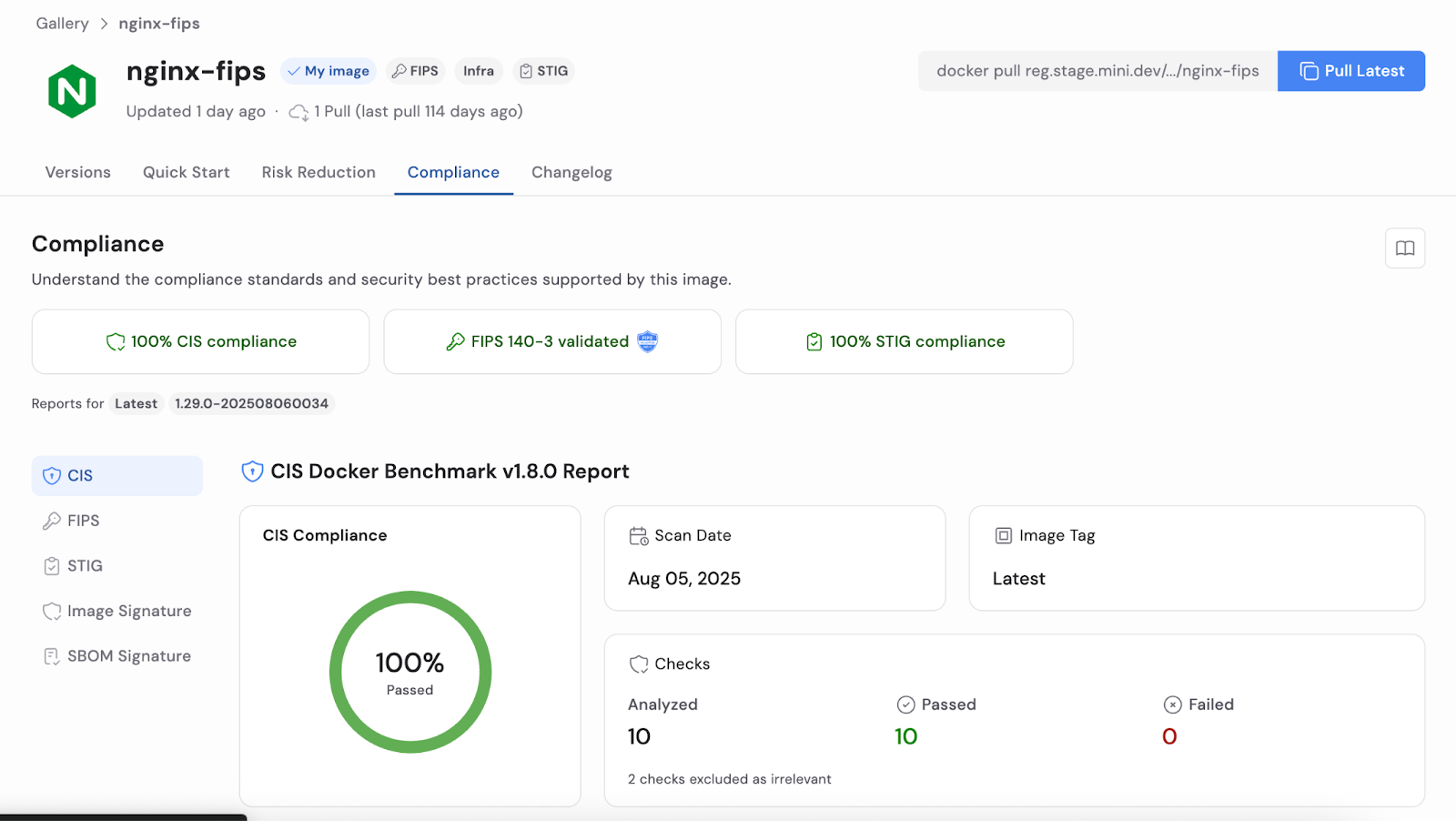
With Minimus images, you get a detailed overview of compliance benchmarks. Organizations that must meet stringent compliance standards, or those that simply want to limit their exposure, can immediately take advantage of this expanded capability when they switch to Minimus images.
Minimus also provides images that require FIPS 140-3 Validation, leveraging the Minimus Cryptographic Module, and how customers can validate and test these images for themselves. We provide the commands needed for every image in our gallery, including private images.

For our customers who need to provide a STIG evaluation report for the images they deploy, this is also included with details about the results and checks.

Minimus continues to provide a comprehensive SBOM for all of its images. Each image is cryptographically signed and can be verified manually or as part of the customer's build process.
All of our images are continually maintained and updated. Customers can integrate Minimus with their existing build infrastructure and security tooling; there is no need to rip out processes and practices that are well understood by teams.
Simply configure notifications or actions for when vulnerabilities are remediated in our images. We’ll integrate seamlessly with your existing infrastructure, build systems, and container registries.
Minimus container images are built to be compliant from the start, maintained continuously, and give you clear compliance data that maps to CIS, FIPS, and STIG. With Minimus’ compliance dashboards, customers have complete visibility into the details needed to report on compliance to other teams and auditors.