Container Security, Built By Those Who Invented It
Deploy and improve security immediately without forcing disruptive re-architecture or other $urprises…


RELIABILITY
Brought to you by the founders of Twistlock
Brought to you by the
guys behind Docker Desktop
Vulnerability
Remediation SLA
Remediation SLA
48 hour
tSLA=Max (Debian, Libc, Musl, GNU...)
Every component, every image, built from source continuously


Images are half the size and attack surface — or less


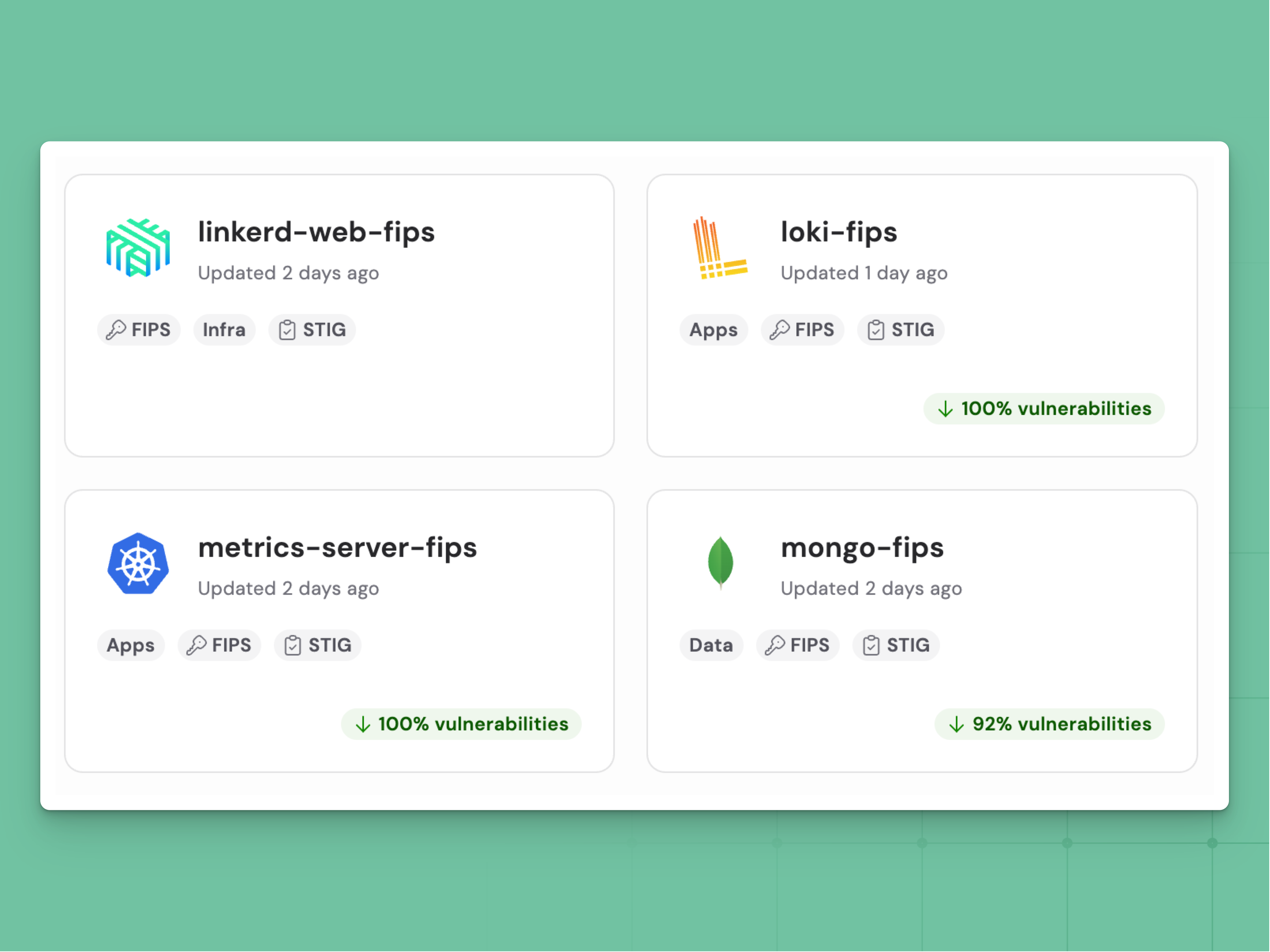
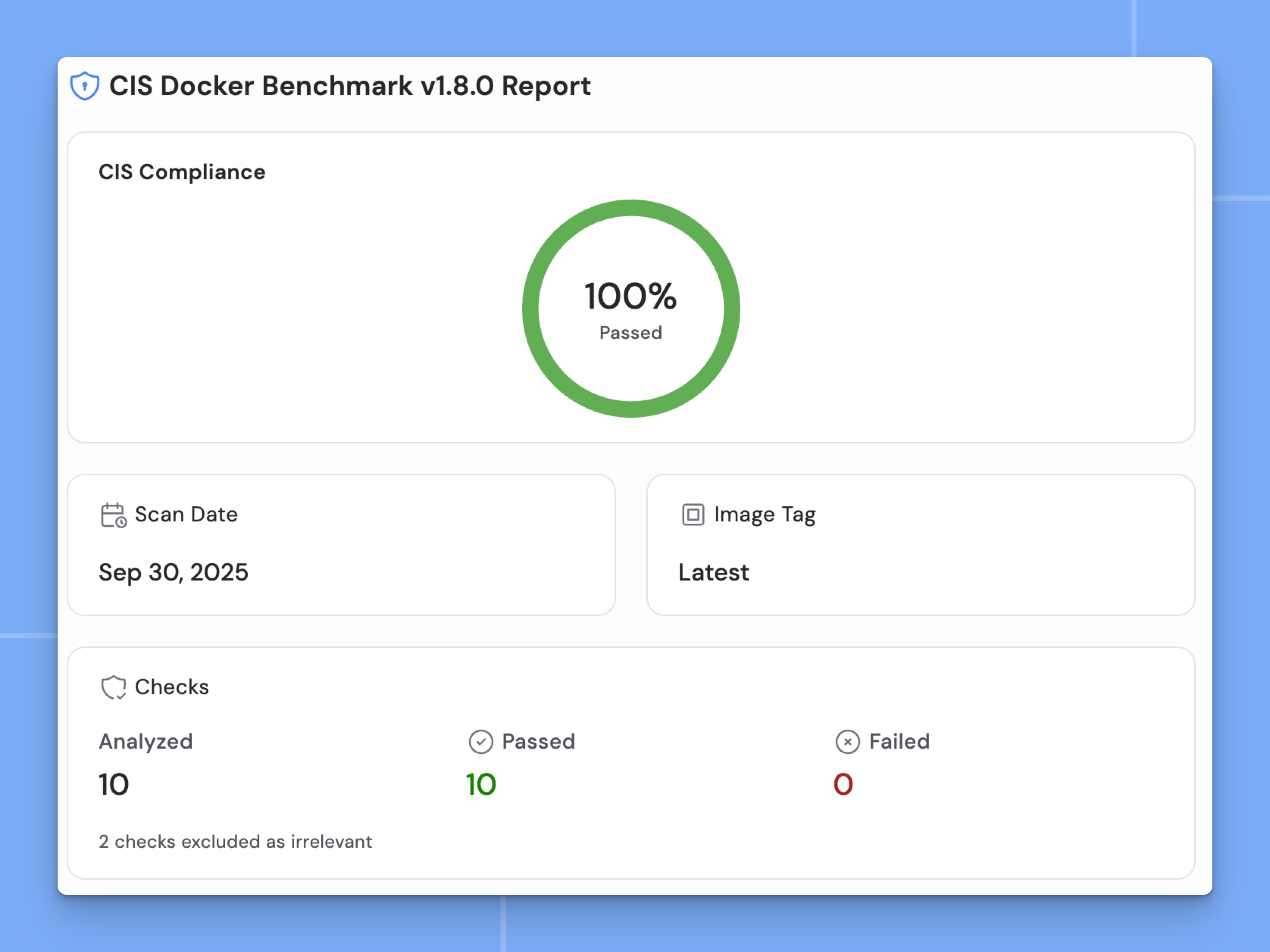
Honest, accurate vulnerability data


Supply chain protection with no blind spots


A CLI built for agents and your CI pipeline


TRUSTED BY GLOBAL MARKET LEADERS


























.svg)
.svg)




.svg)




.svg)

